What is ExtendedKeyUsage?
 Rachel Acosta
Rachel Acosta 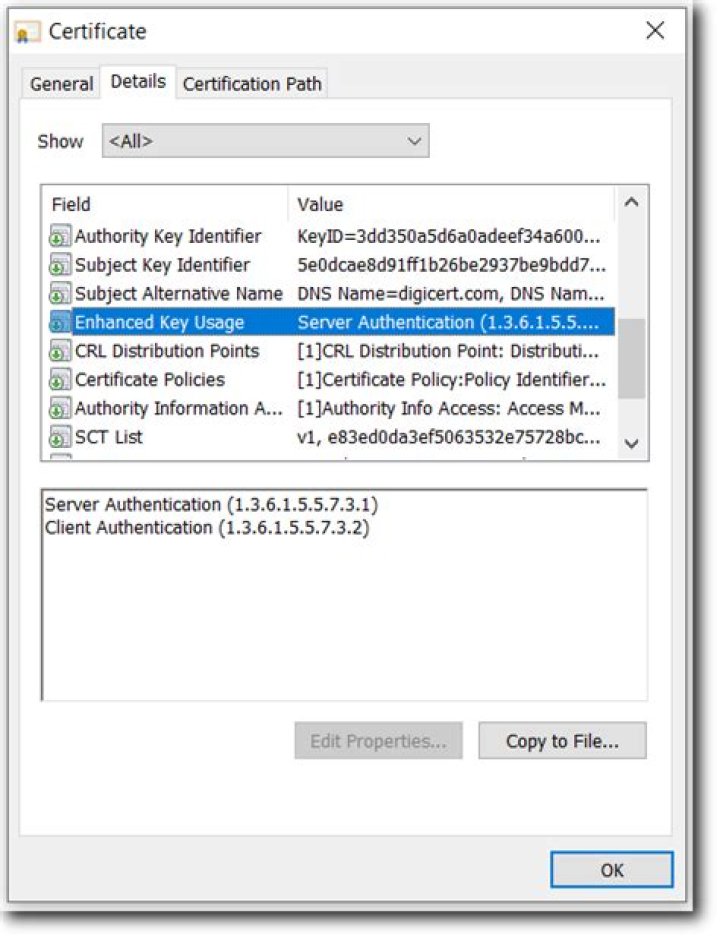
ExtendedKeyUsage is a Certificate Extensions and consists of a list of usages indicating purposes for which the certificate public key can be used for. These can either be object short names of the dotted numerical form of OIDs. While any OID can be used only certain values make sense.
What is certificate Extended key Usage?
Extended key usageThis extension indicates one or more purposes for which the certified public key may be used, in addition to or in place of the basic purposes indicated in the key usage extension.
What is key usage digital signature?
Key usage extension. Description. Digital signature. Use when the public key is used with a digital signature mechanism to support security services other than non-repudiation, certificate signing, or CRL signing. A digital signature is often used for entity authentication and data origin authentication with integrity.What is key usage?
KeyUsage is a Certificate Extensions and defined in RFC 5280 in regards to X. 509 Certificate defines the purpose (e.g., encipherment, signature, certificate signing) of the key contained in the certificate.What does key Usage Critical mean?
A “Critical Extension” or “Criticality Indicator” is a flag that instructs software that uses the certificate where it is safe to ignore the Extended Key Usage Extension if it does not recognize it.Masterclass in openSSL
How do you know if a certificate is being used?
Chrome has made it simple for any site visitor to get certificate information with just a few clicks:
- Click the padlock icon in the address bar for the website.
- Click on Certificate (Valid) in the pop-up.
- Check the Valid from dates to validate the SSL certificate is current.
What is root certificate and CA certificate?
A Root CA is a Certificate Authority that owns one or more trusted roots. That means that they have roots in the trust stores of the major browsers. Intermediate CAs or Sub CAs are Certificate Authorities that issue off an intermediate root.What is TLS Web client authentication?
The Transport Layer Security (TLS) is a protocol designed to provide secure communication over the Internet and includes authentication, confidentiality and integrity. When a TLS connection is established the server provides a certificate that the client validates before trusting the server's identity.What is EKU client authentication?
It is a type of extension that includes a list of usage to which the public key can be applied. The EKU extension is included in a certificate and shows with a separate OID and meaning of field as shown below: Server authentication (OID 1.3. 6.1. 5.5.What is SubjectAltName Openssl?
Subject Alternative Names are a X509 Version 3 (RFC 2459) extension to allow an SSL certificate to specify multiple names that the certificate should match. SubjectAltName can contain email addresses, IP addresses, regular DNS host names, etc. This uses an SSL feature called SubjectAlternativeName (or SAN, for short).How is a digital signature created?
A digital signature is created using hash algorithms or a scheme of algorithms like DSA and RSA that use public key and private key encryptions. The sender uses the private key to sign the message digest (not the data), and when they do, it forms a digital thumbprint to send the data.What is subject key identifier in certificate?
The subject key identifier (SKID) is an x509 extension and thus actually part of the certificate. The fingerprint instead is not part of the certificate but instead computed from the certificate. A certificate does not need to have an SKID at all and can have at most one SKID.What is DataEncipherment?
DataEncipherment is a KeyUsage bit that is asserted when the Certificate Subject Public Key is used for direct Encryption of raw user data without the use of an intermediate symmetric cipher. Note that the use of this bit is extremely uncommon; almost all use Key-Exchange or Key agreement to establish a Symmetric Key.What is difference between client and server certificate?
Client certificates tend to be used within private organizations to authenticate requests to remote servers. Whereas server certificates are more commonly known as TLS/SSL certificates and are used to protect servers and web domains.Why do servers use certificates?
A server certificate is used to authenticate the server's identity to the client. A client certificate is used to authenticate the client or user identity to the server. Server certificates perform encryption on data-in-transit to assure data confidentiality.What are the SSL certificate types?
What are the different types of SSL certificates?
- Single Domain SSL Certificates. ...
- Wildcard SSL Certificates. ...
- Multi-Domain SSL Certificates (MDC) ...
- Domain Validation SSL Certificates. ...
- Organization Validation SSL Certificates. ...
- Extended Validation SSL Certificates.